What MSPs Should Look For In A Vulnerability Management Solution
The right vulnerability management (VM) solution can give managed service providers (MSPs) an edge over the competition. Not only does it provide full insights into their own vulnerabilities (and the ability to remediate them), it also adds a powerful service that their clients and prospects need from both a security and compliance standpoint.
If you are an MSP in the process of building cyber resilience, you have likely considered the potential benefits of adding vulnerability management to your portfolio. The rapidly evolving threat landscape has pushed cybersecurity to the forefront of priorities. Companies must shore up their cybersecurity postures or risk being put out of business, the MSP Expo cautions. This fact presents a business opportunity.
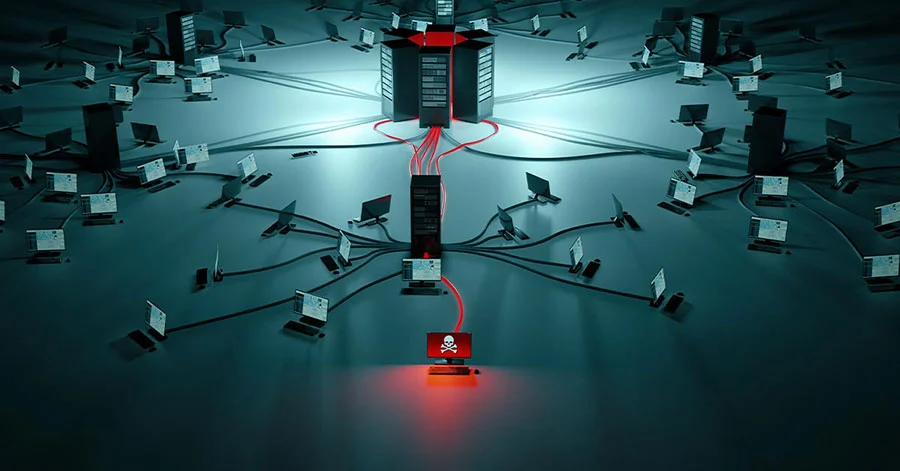
The question is: How equipped are you to identify, assess, and remediate vulnerabilities in systems that include far more than the networks and private hosted applications of the past? Attack surfaces keep expanding, forcing organizations to consider risks associated with Internet of Things (IoT), cloud applications, complex digital supply chains, and more.
How do you know which vulnerability management solution is right for you — and your clients?
A few features stand out:
The features of an effective solution
Ability to discover — and perform recurring scans of all IT assets
Gartner points out vulnerability assessment is a function that can be delivered via active scanning, agents and passive monitors, and recommends that organizations leverage a combination of all of the above for complete coverage. Although Gartner tends to focus on enterprises, the importance of breadth of coverage holds true for MSPs and their small-to-medium-sized clients (SMBs) too.
Any asset discovery process and vulnerability assessment must achieve full visibility; in other words, the solution needs to identify and continuously scan all assets in your environment to eliminate any risk of blind spots.
This means the solution must take into account the proliferation of IoT devices as well as a growing number of people working from home on a full- or part-time basis. External scans show weaknesses in a network that could lead to a potential incident by helping to detect open ports, protocols, and named vulnerabilities in public-facing network equipment such as web servers and firewalls.
At the heart of this process is the vulnerability scanner which should have the capability to discover systems running on your network or that connect via remote access solutions, including:
- laptops and desktops
- virtual and physical servers
- databases
- firewalls
- printers
- routers
- access points
- switches
- IoT devices
Once detected, the scan probes each system for attributes, such as operating systems, open ports, installed software, user accounts, file system structure, system configurations, and more. In order to determine whether they are vulnerable to attack, the information is run through several databases of publicly known vulnerabilities, such as NIST’s National Vulnerability Database (NVD) and OEM sources. The results determine what actions should come next (see more below).
Alignment with the NIST Cybersecurity Framework and other important compliance standards
According to the NIST Cybersecurity Framework, the cybersecurity journey of any business starts with the “Identify” stage (the four other functions include: protect, detect, respond, recover), which establishes the foundation for future success in protecting an IT environment. In short, it's a framework that businesses should pay close attention to.
The quickest way to detect vulnerabilities and securing networks? Run an assessment that scans your own and your customer’s IT infrastructure for this common compliance standard.
NIST states: “The Identify Function assists in developing an organizational understanding to managing cybersecurity risk to systems, people, assets, data, and capabilities. Understanding the business context, the resources that support critical functions, and the related cybersecurity risks enables an organization to focus and prioritize its efforts, consistent with its risk management strategy and business needs.”
While you can introduce the benefits of NIST compliance to your end customers, the right vulnerability management solution gives you the ability to support other standards as well. Depending on which industries your clients are in, they will benefit from your support for compliance standards like PCI DSS, HIPAA, GDPR IV, NIST 800-53, NIST 800-171, CIS, CIS 8.0, ISO 27002, Cyber Essentials and Essential Eight.
Ease of use and easy-to-understand reporting that clearly articulates risk to the business for end customers
Whether you want to build customized reports with a user-friendly drag-and-drop editor or have data automatically presented, your vulnerability management solution should not make you choose. Easy-to-understand reporting is essential to busy MSPs. The ability to clearly articulate business risk is a key piece of how you can bring value to your end customers; and an actionable and intuitive dashboard that shows what needs to be addressed can help you achieve that goal.
The ease of reporting should cover every aspect of the Identify stage of the NIST Cybersecurity Framework, allowing you to present a range of reports in standard Microsoft Office formats (Word, Excel, PowerPoint), such as:
- Asset reports
- Vulnerability reports
- Compliance reports
- Remediation reports
- Security posture reports
- Active directory reports: identifying misconfigurations, weak policies, and privilege user access
- Build your own
TechTarget observes: “A vulnerability management tool must be easy to deploy and use, reliable, nonintrusive and safe — that is, it poses few conflicts for an existing IT environment. A product that is cumbersome to navigate or presents confusing dashboard information won't be used, at least not to its fullest potential.”
Key features of an easy-to-use solution include, for instance:
- Integration to industry standard PSA systems
- Availability of a one-time scan which opens an opportunity to talk about risk with your customer
- Multi-tenant view to all MSP clients
- Strong role and access-based security for co-managed clients
Ability to prioritize remediation of vulnerabilities
Just showing customers their vulnerability risk exposure is no longer sufficient. As important is having the ability to mitigate those risks. Not all, however, bring the same risk of exploitation. Therefore, consider a solution that, once you have identified the threats, lets you categorize them based on their potential impact if you were to face a cyberattack.
Ratings and scores, such as Common Vulnerability Scoring System (CVSS), an open framework for communicating the characteristics and severity of software vulnerabilities, inform the evaluation and determine which vulnerabilities should take priority. The scores are not a catch all but one of many factors that contribute to accurate vulnerability identification with low false positive rates. Given the broad data sets analyzed, effective prioritization is crucial to addressing risks with the highest likelihood of exploitation in the near future.
Look for a solution that includes an Application Patching feature that helps remediate vulnerability by patching third-party Windows applications. This greatly helps reduce risk exposure and serves to safeguard the network from external actors. To cite Gartner, organizations that leverage risk-based vulnerability management will suffer 80% fewer breaches.
Final word
As the threat landscape grows more complex, MSPs have an unprecedented opportunity to introduce the importance of building cyber resilience to their SMB customers. Just as using firewalls and virus software has become second nature to businesses, vulnerability management will be an indispensable feature of the future. The cost of leaving business networks exposed is simply too high.
Read more:
What role does vulnerability management play in cyber insurance?
Q&A: Attorney Eric Tilds on what MSPs should know about cyber insurance

