
Simplified vulnerability scanning and compliance management for IT teams
Protect every user. Everywhere.
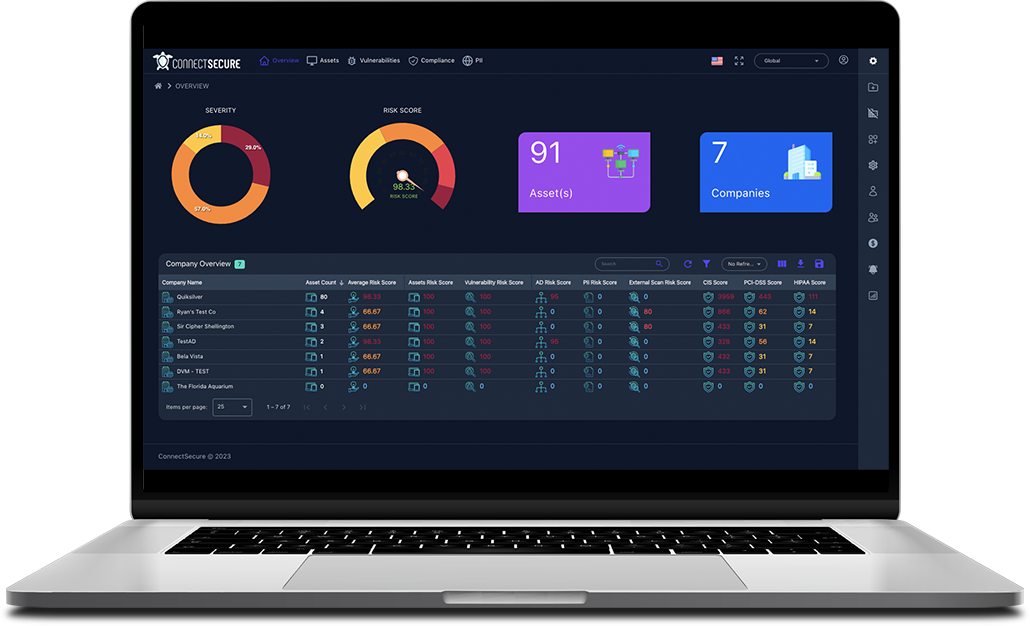
Manage vulnerabilities, patching, and compliance from one platform that gives you more visibility. And more control.
Simplified vulnerability scanning and compliance management for IT teams
Protect every user. Everywhere.
Manage vulnerabilities, patching, and compliance from one platform that gives you more visibility. And more control.
Certified for security, privacy, and reliability



Maintaining visibility and compliance takes a lot of time. And a lot of effort.
So many assets. So much risk. So much at stake.
Auditors and insurers need proof. But that takes time.
Too many tools. Too many headaches. Too many fees.
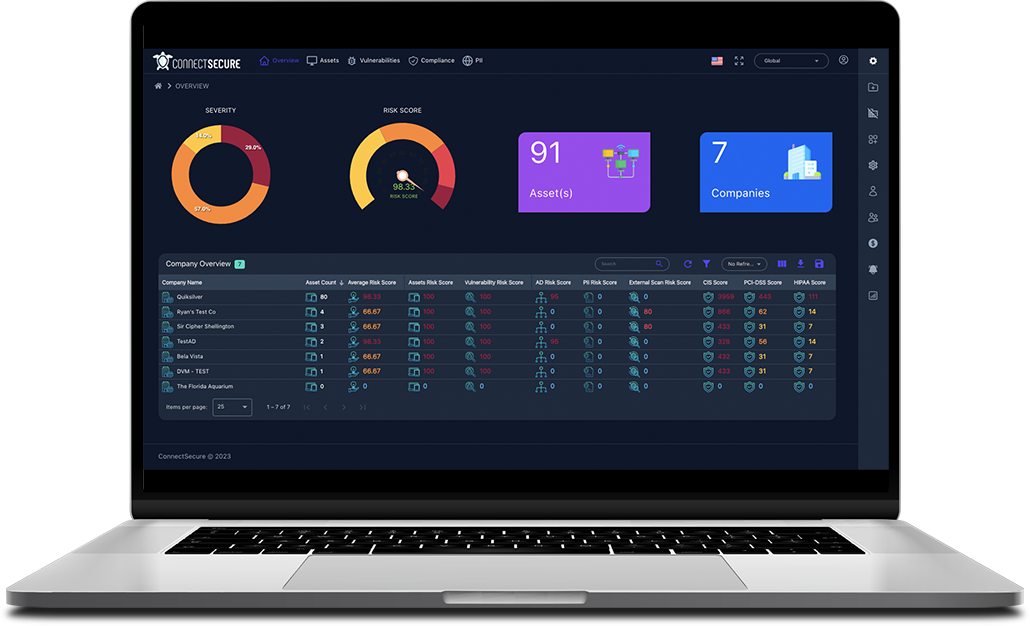
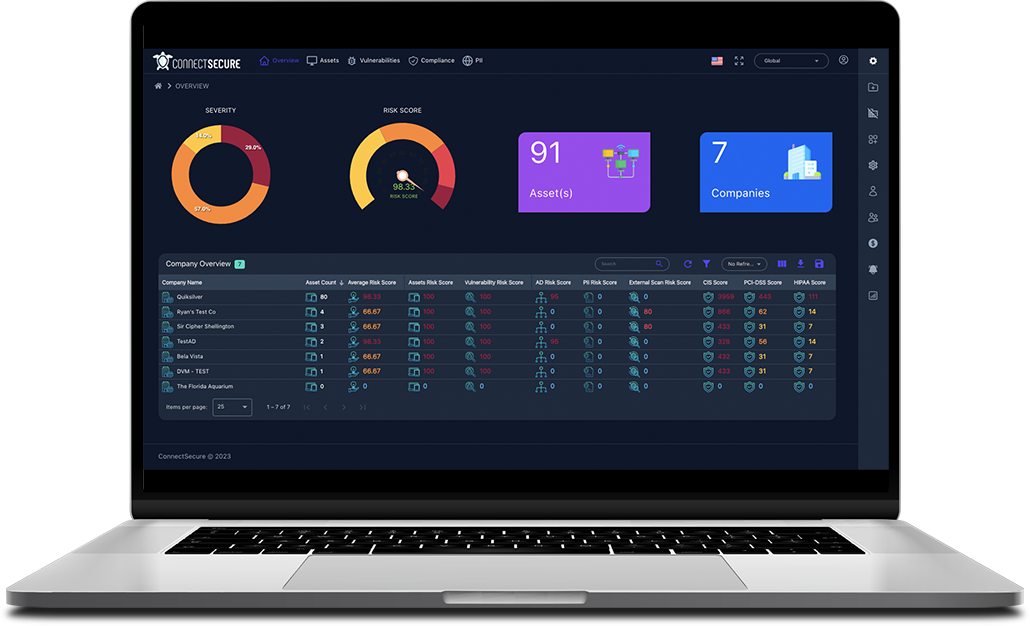
Get more visibility and control from one simplified vulnerability and compliance solution
See every internal and external asset
From core infrastructure to third-party apps.Prove you’re managing vulnerabilities
Show a clear, defensible process to auditors and insurers.Set up regular scans
Schedule scans and reports, trigger alerts for critical changes.Know exactly what to fix
Prioritize long lists of CVEs into easy next steps.Create reports for every audience
Detailed remediation plans. High-level updates. Audit-ready proof.Securing over

&
worldwide
Try ConnectSecure free for 14 days.
Partners get the most affordable, high-value vulnerability scanning and compliance management out there.
Get complete visibility over all vulnerabilities. All in one place.
Applications
Detect vulnerabilities in software and third-party apps beyond what basic patching reports surface.
Operating Systems
Track vulnerabilities and missing updates across Windows, macOS, and Linux systems.Network
Find firewall weaknesses, open ports, exposed services, and protocol issues across networks and devices.Registry
Identify insecure or vulnerable Windows registry settings tied to known risks and benchmarks.Drivers
See outdated or vulnerable drivers across endpoints, systems, and devices.Access Controls
Identify weak passwords, excessive privileges, insecure configurations, and more.Cryptographic
Surface weak or outdated encryption, cipher issues, and certificate problems across your environment.Third-party and Supply Chain
See risks introduced by external services, vendors, SaaS platforms, and more.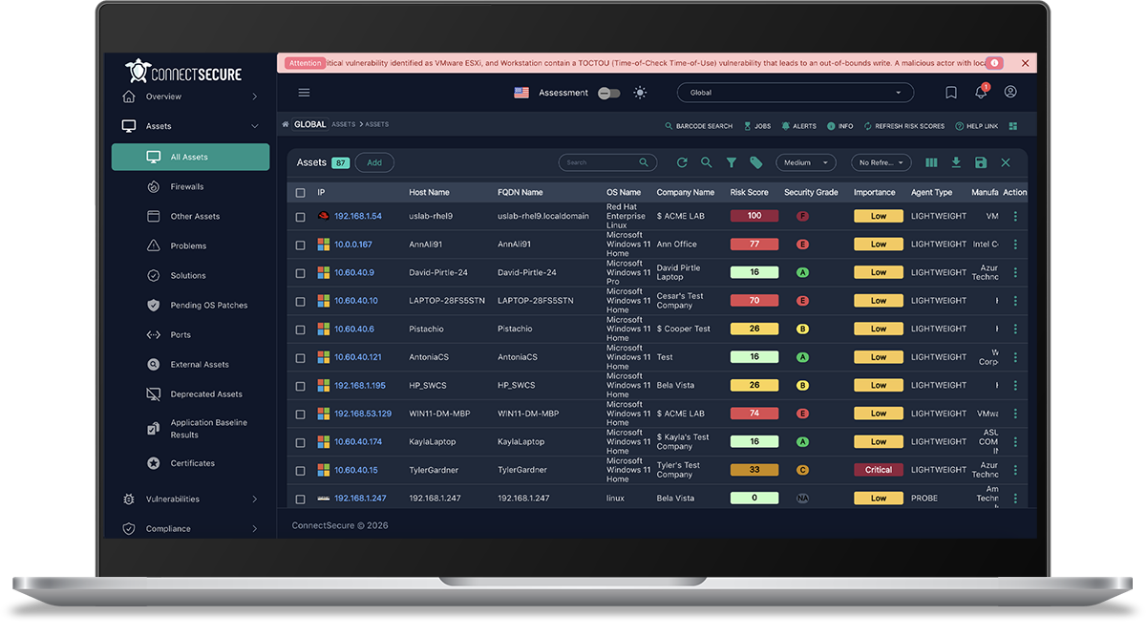
IDENTIFY
You can’t secure what you can’t see. Until now.
Identify the entire attack surface
Discover endpoints, network devices, and unmanaged assets that aren’t visible in your existing tools. See what’s connected, what’s exposed, and what’s been missed.
Find the blind spots in your network
Unmanaged devices, unknown assets, and misconfigured systems create gaps that attackers can easily exploit. ConnectSecure helps you uncover what’s out there so you can take control.
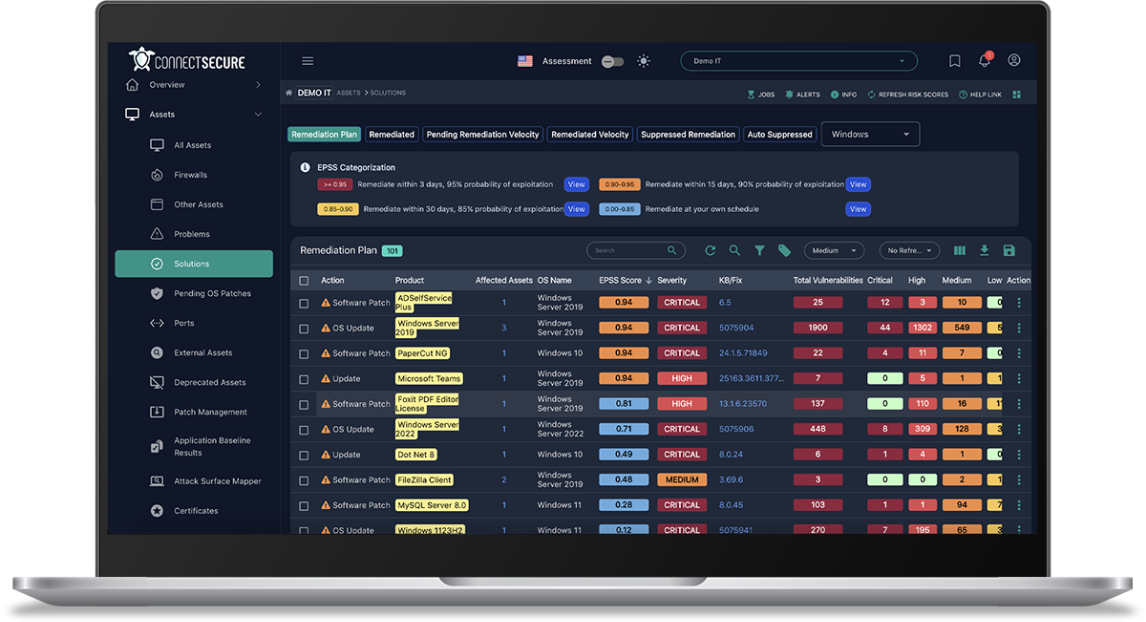
PATCH
Remediate issues faster with built-in remediation
Go straight from finding to fixing
Apply updates, configuration changes, or removals, without bouncing between tabs.
Patch what matters, automatically
Update operating systems and 550+ third-party apps automatically. No more chasing down updates.
Handle complex fixes without extra work
Run scripts and registry fixes directly from the platform
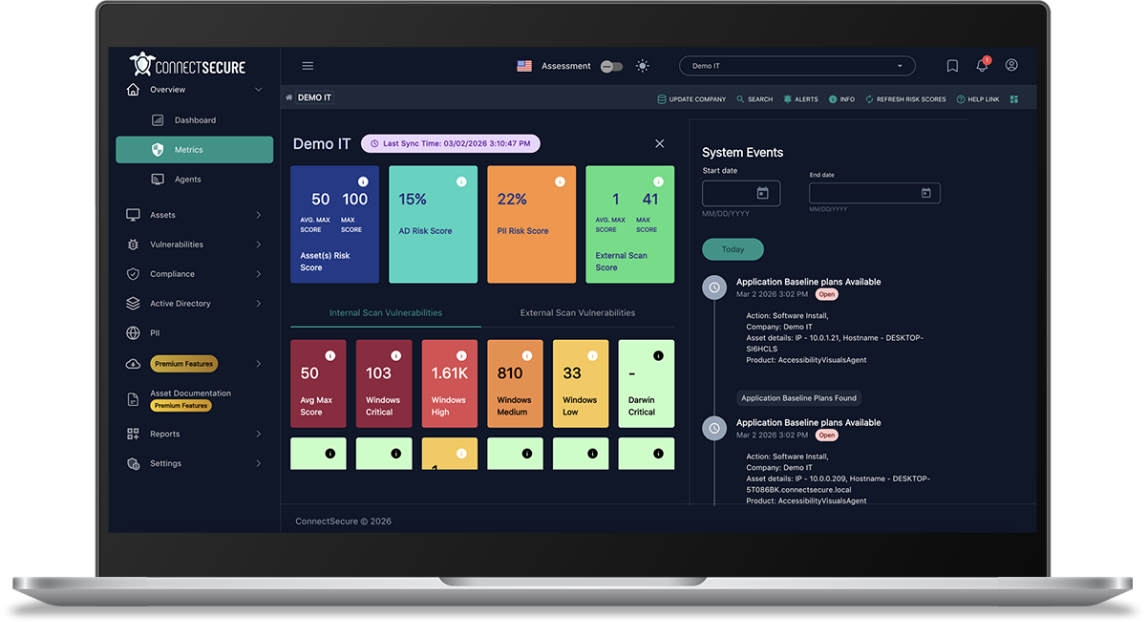
MONITOR
Never get caught off guard again
Get the complete visibility you need to protect users
Continuously track vulnerabilities, compliance status, and potential exposures.
Know when to act
Get alerted when critical-severity vulnerabilities are detected.
Cut through the noise
Filter thousands of vulnerabilities across your environment, with direct links to the fix and clear next steps.
Focus on what matters
Prioritize issues by exploitability, business impact, and risk.
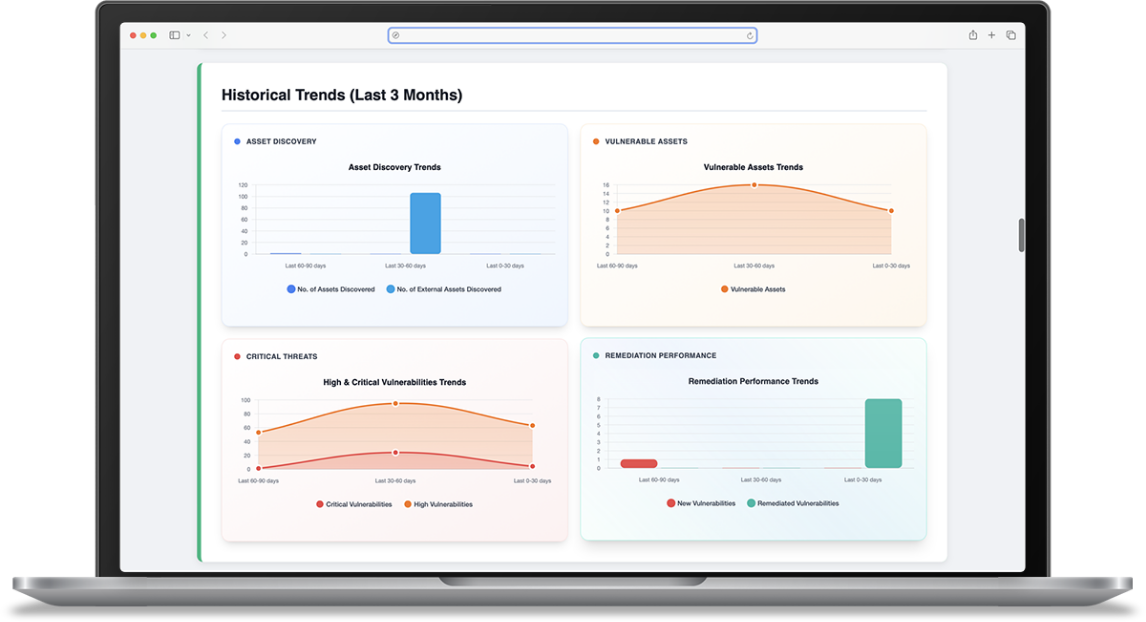
REPORT
Turn vulnerability and compliance data into clear reports for teams, auditors and insurers
Create reports for every audience
Generate executive summaries, remediation-ready reports, and audit-ready documentation.
Show progress and justify decisions
Use vulnerability trends and remediation history to show improvement over time and explain what was prioritized, why it mattered, and how quickly issues were addressed.
Deliver reports automatically
Schedule reports to be sent on a regular cadence so audits don’t turn into fire drills.
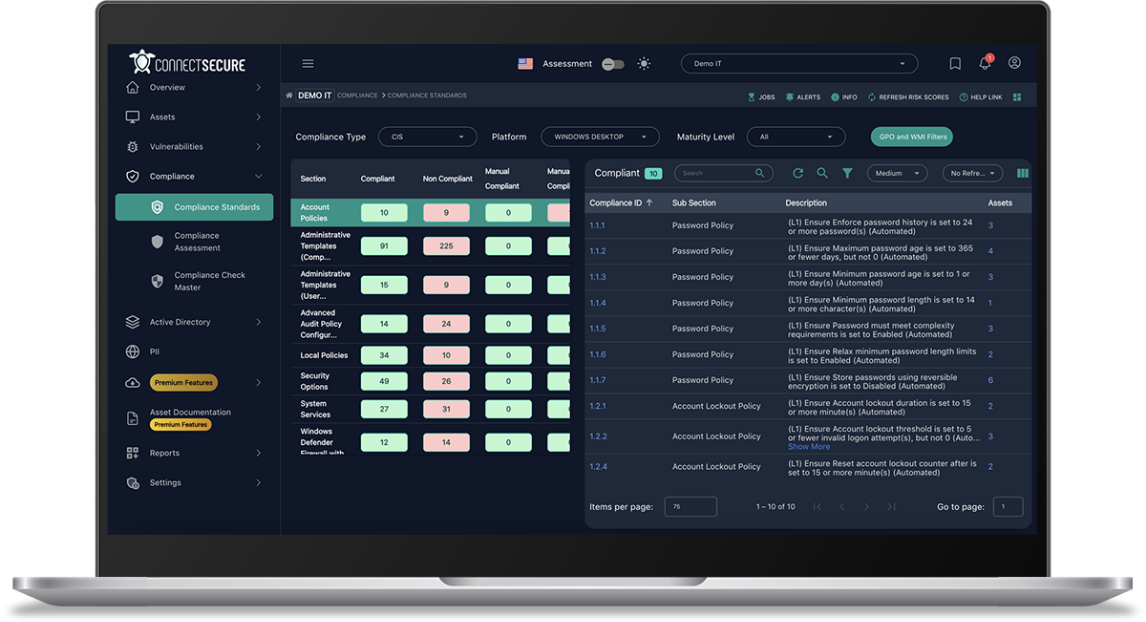
COMPLIANCE
See your compliance, insurance, and third-party security posture in one place
Find compliance gaps (before auditors or insurers do)
Surface misconfigurations, missing control safeguards, and unmanaged risk that could lead to fines or insurance issues.
ConnectSecure aligns vulnerability scanning with frameworks like NIST, CIS, Cyber Essentials, HIPAA, and more. So you’re focused on what insurers and auditors actually care about.
Save time with built-in compliance remediation
Fix common issues with built-in framework templates. Get step-by-step guidance for manual fixes. And easily deploy policies through GPO and WMI filters.
Catch compliance drift before it becomes a violation
Track compliance over time and get alerted when configurations or controls drift out of alignment.
Secure Microsoft 365 with CIS benchmarks
Assess configurations, permissions, and identity risk across M365 and align them to CIS security benchmarks, without relying on Secure Score alone.
See external risks before they become internal problems
Monitor vulnerabilities in third-party apps
Use the Web Application Scanner to passively scan the mission-critical tools employees use every day, including CRMs, accounting and marketing tools, and more.
You can also use it to scan your websites, web portals, and other internet-facing applications.
See vulnerabilities like cross-site scripting (XSS), remote code execution (RCE), SQL injection, and other issues that put your environment at risk.
Verify that ISO-certified services are operating the way the standard expects.
See potential problems in external assets
See potential problems in external assets
Scan internet-facing IPs and ranges to understand what’s exposed outside your direct control.
See certificate and cipher issues, open or filtered ports, detected vulnerabilities, and any OS or fingerprinting details that can be identified.
Scan externally. No agents. No installs. No maintenance.
Just provide a target, and the platform scans it remotely across your environments.
Get fast visibility into external risks that your team can immediately prioritize and remediate.
Start making vulnerability scanning and compliance management easier today
Your trial is fully functional and includes everything in our platform:
- Asset inventory and tagging
- Continuous vulnerability management
- Active Directory and Entra ID scanning
- External asset scanning
- Attack surface mapper
- Operating system patching
- Third-party application patching
- Cyber risk assessment
- Compliance control assessment
- Application baseline audit
- Cloud Assessments
- Web Application Scanning
- EPSS, CVSS, and CISA KEV prioritization
- 80+ pre-built dashboards
- 100+ role-based and white-label reports
- Scan, patch, and report schedulers
- 30+ integrations
- PII Scanning
- Software Asset Inventory
- Alerting
Start scanning in minutes
Frequently asked questions about ConnectSecure for enterprise IT
Which operating systems do you support?
We can scan Windows, macOS, Linux, and ARM-based operating systems.
Operating system patching is supported on Windows and Linux OS.
We also support 550+ Windows application patches.
Can you help me make the case to leadership that we should use ConnectSecure?
Frame it as risk reduction and cost avoidance.
ConnectSecure helps lower the likelihood of a costly security incident by continuously scanning for weaknesses, prioritizing what matters, and fixing issues before they’re exploited.
That means fewer emergency recoveries, fewer insurance complications, and less reputational damage.
It’s far less expensive to prevent problems than to respond to them. This gives you a proactive way to reduce risk instead of reacting after something breaks.
How much information is available in the asset view?
In the asset view, you can see all machines in your environment, with IP addresses, hostnames, Security Grades, and vulnerability metric. You can also see their hardware/software inventory, services, ports, protocols, vulnerabilities, compliance status for each asset, and more.
Click into a single asset to see the full depth of available data. There’s system information, individual vulnerability lists, and associated solutions.
You can also see port inventories and software inventories.
There are also report cards covering baseline security items such as antivirus, anti-ransomware, supported operating systems, local firewalls, SMB versions, and TLS settings.
If you need more detail on a specific CVE, you can go straight to the vulnerability database and see how long it’s been present in the environment.
Some users have admin rights (despite my objections). Can you help me stay in control?
It happens. We have your back. Our audit log records all moves, additions, changes, and deletions.
Is this a replacement for penetration testing?
No, and it’s not trying to be.
ConnectSecure doesn’t perform full, human-led penetration tests.
What it does give you is visibility into vulnerabilities like open ports, exposed services, weak ciphers, and configuration issues across internal and external assets and websites.
There’s also a web application scanner that can go deeper on public-facing apps.
These insights can help you prepare for a PEN test. Rather than spend thousands only to be told something basic wasn’t patched.
How heavy is the agent?
It’s lightweight.
On average, the endpoint agent uses about 25 MB of memory. Usage can increase slightly if you enable extended scan times or PII scanning. If there is a spike, it usually lasts only a few minutes because scans complete quickly.
There are two agent types:
The lightweight agent, which runs on the machine itself and scans that device.
The probe, which scans the network. It’s used for asset discovery and finding vulnerabilities on devices that don’t have agents, like printers, switches, routers, and other IoT devices.
The probe also supports network discovery, vulnerability and compliance scans, SNMP scans, and internal firewall scanning.
In smaller environments, one probe is usually enough. Larger networks may benefit from two or three to distribute load.
What if I have questions or need help?
During your free trial, our Solutions Engineers will help you configure ConnectSecure to your environment and compliance requirements so you start seeing value quickly.
As a partner, you’ll also get one-on-one onboarding, help building vulnerability policies and SOPs, and guidance on remediation timelines.
Documentation is available when you need quick answers. If you need more, our US-based support team is ready to jump in and help resolve it. Just send us a message, open a ticket, or start a chat.
Start your free 14-day trial. No credit card required.
You get full access, guided onboarding and all the documentation you need to secure every asset and environment you manage.
No pressure. Just a chance to see how ConnectSecure keeps organizations secure and compliant — with less stress and less effort.